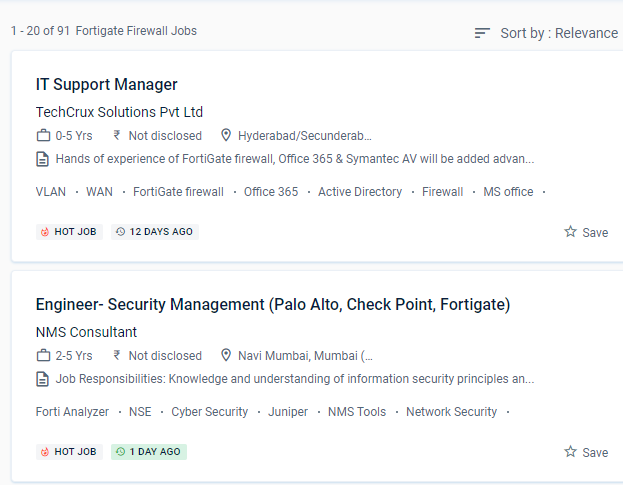
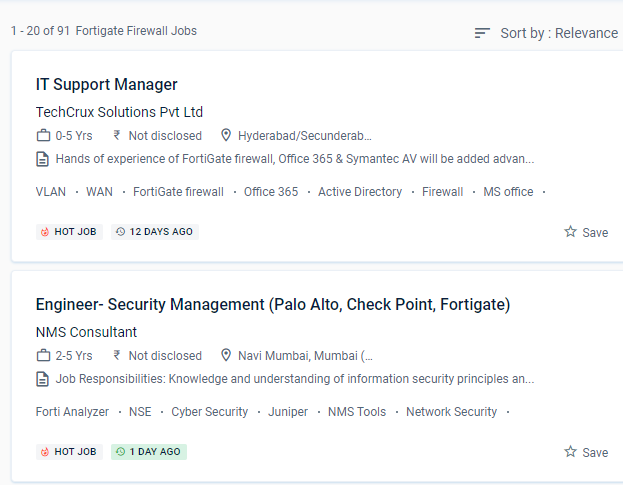
Fortinet Firewall Internship/Course Details

Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt. According to the latest Anti-Phishing Working Group (APWG) report, SSL was employed by 75% of all phishing sites in the first quarter of 2020.
Firewall policies are used to control network access to configured networks.
For administration, use the GUI and CLI.
Based on the Fortinet course in Kottayam learn how to manage setup, monitoring, and operations with FortiGate appliances. This system may be customized to fit any business environment while preserving cutting-edge security features.
Gather and analyze log entries
.
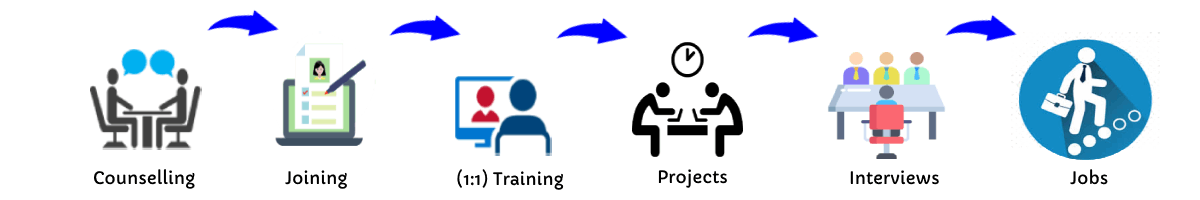
After completing the course from Kottayam you should be able to: Implement the right mode of operation for your network after completing this course.
This course gives students from all over the world industry-recognized Fortinet training and certification options, allowing them to join an exclusive group of cybersecurity professionals.


 Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt. According to the latest Anti-Phishing Working Group (APWG) report, SSL was employed by 75% of all phishing sites in the first quarter of 2020.
Firewall policies are used to control network access to configured networks.
For administration, use the GUI and CLI.
Based on the Fortinet course in Kottayam learn how to manage setup, monitoring, and operations with FortiGate appliances. This system may be customized to fit any business environment while preserving cutting-edge security features.
Gather and analyze log entries
.
After completing the course from Kottayam you should be able to: Implement the right mode of operation for your network after completing this course.
This course gives students from all over the world industry-recognized Fortinet training and certification options, allowing them to join an exclusive group of cybersecurity professionals.
Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt. According to the latest Anti-Phishing Working Group (APWG) report, SSL was employed by 75% of all phishing sites in the first quarter of 2020.
Firewall policies are used to control network access to configured networks.
For administration, use the GUI and CLI.
Based on the Fortinet course in Kottayam learn how to manage setup, monitoring, and operations with FortiGate appliances. This system may be customized to fit any business environment while preserving cutting-edge security features.
Gather and analyze log entries
.
After completing the course from Kottayam you should be able to: Implement the right mode of operation for your network after completing this course.
This course gives students from all over the world industry-recognized Fortinet training and certification options, allowing them to join an exclusive group of cybersecurity professionals.