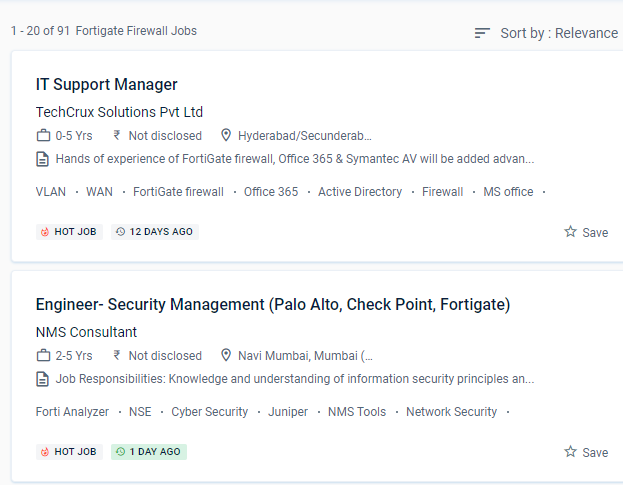
Fortinet Firewall Internship/Course Details

Defeat piracy and denial-of-service attacks (DoS)
For safe admission to your private system, provide an SSL VPN. Rather than being borderless, networks have become porous, with unprecedented numbers of points of access and endpoints.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. This system may be customized to fit any business environment while preserving cutting-edge security features. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt.
Firewall policies are used to authenticate users.
Identify the Fortinet Security Fabric's features.
Firewall policies are used to control network access to configured networks.
Examine SSL/TLS-protected communication for evidence of encryption being used to circumvent security restrictions.


 Defeat piracy and denial-of-service attacks (DoS)
For safe admission to your private system, provide an SSL VPN. Rather than being borderless, networks have become porous, with unprecedented numbers of points of access and endpoints.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. This system may be customized to fit any business environment while preserving cutting-edge security features. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt.
Firewall policies are used to authenticate users.
Identify the Fortinet Security Fabric's features.
Firewall policies are used to control network access to configured networks.
Examine SSL/TLS-protected communication for evidence of encryption being used to circumvent security restrictions.
Defeat piracy and denial-of-service attacks (DoS)
For safe admission to your private system, provide an SSL VPN. Rather than being borderless, networks have become porous, with unprecedented numbers of points of access and endpoints.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. This system may be customized to fit any business environment while preserving cutting-edge security features. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt.
Firewall policies are used to authenticate users.
Identify the Fortinet Security Fabric's features.
Firewall policies are used to control network access to configured networks.
Examine SSL/TLS-protected communication for evidence of encryption being used to circumvent security restrictions.