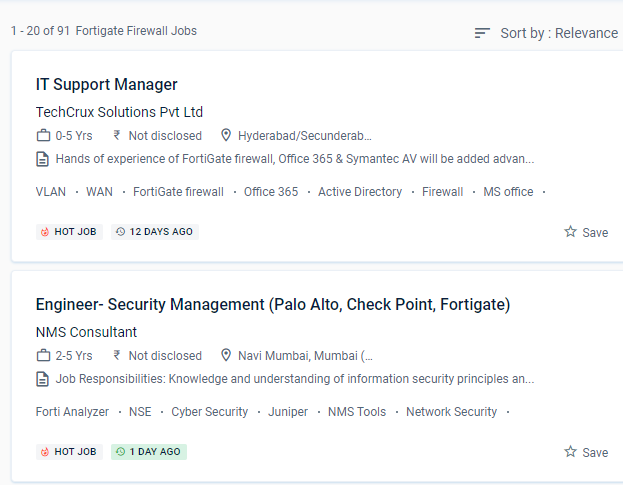
Fortinet Firewall Internship/Course Details

Firewall policies are used to control network access to configured networks. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt. And, as malware and threats grow more difficult to detect at the access point, security must be extended across the network to monitor behaviors and reveal intent. This system may be customized to fit any business environment while preserving cutting-edge security features.
Understand the responsibilities of encryption and certificates. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention.
For administration, use the GUI and CLI.
It is the most widely used security appliance from Fortinet, and it provides Unified Threat Management via a platform that incorporates both physical and virtual security appliances. Rather than being borderless, networks have become porous, with unprecedented numbers of points of access and endpoints.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation.


 Firewall policies are used to control network access to configured networks. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt. And, as malware and threats grow more difficult to detect at the access point, security must be extended across the network to monitor behaviors and reveal intent. This system may be customized to fit any business environment while preserving cutting-edge security features.
Understand the responsibilities of encryption and certificates. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention.
For administration, use the GUI and CLI.
It is the most widely used security appliance from Fortinet, and it provides Unified Threat Management via a platform that incorporates both physical and virtual security appliances. Rather than being borderless, networks have become porous, with unprecedented numbers of points of access and endpoints.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation.
Firewall policies are used to control network access to configured networks. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt. And, as malware and threats grow more difficult to detect at the access point, security must be extended across the network to monitor behaviors and reveal intent. This system may be customized to fit any business environment while preserving cutting-edge security features.
Understand the responsibilities of encryption and certificates. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention.
For administration, use the GUI and CLI.
It is the most widely used security appliance from Fortinet, and it provides Unified Threat Management via a platform that incorporates both physical and virtual security appliances. Rather than being borderless, networks have become porous, with unprecedented numbers of points of access and endpoints.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation.