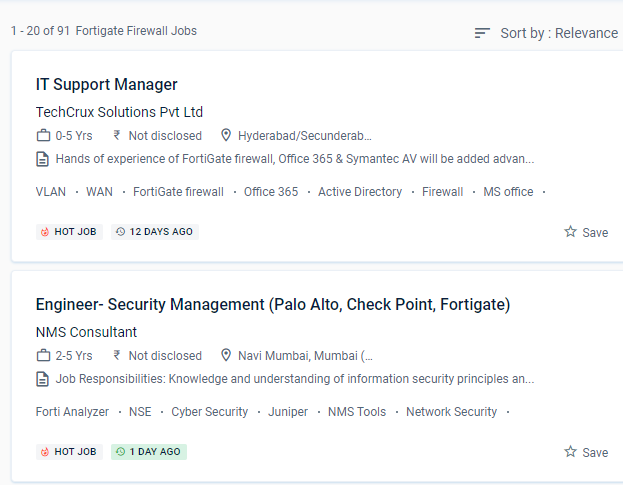
Fortinet Firewall Internship/Course Details

NESTSOFT train IT and Fortinet ecosystem workers in information, configuration, and management to safeguard networks of enterprises whose most valuable asset is their data.
Use port forwarding, source NAT, and destination NAT to your advantage.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt.
Understand the responsibilities of encryption and certificates. And, as malware and threats grow more difficult to detect at the access point, security must be extended across the network to monitor behaviors and reveal intent.
For administration, use the GUI and CLI. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. Prepare the professional for the implementation of corporate security policies and the strengthening of network security programs. According to the latest Anti-Phishing Working Group (APWG) report, SSL was employed by 75% of all phishing sites in the first quarter of 2020.


 NESTSOFT train IT and Fortinet ecosystem workers in information, configuration, and management to safeguard networks of enterprises whose most valuable asset is their data.
Use port forwarding, source NAT, and destination NAT to your advantage.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt.
Understand the responsibilities of encryption and certificates. And, as malware and threats grow more difficult to detect at the access point, security must be extended across the network to monitor behaviors and reveal intent.
For administration, use the GUI and CLI. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. Prepare the professional for the implementation of corporate security policies and the strengthening of network security programs. According to the latest Anti-Phishing Working Group (APWG) report, SSL was employed by 75% of all phishing sites in the first quarter of 2020.
NESTSOFT train IT and Fortinet ecosystem workers in information, configuration, and management to safeguard networks of enterprises whose most valuable asset is their data.
Use port forwarding, source NAT, and destination NAT to your advantage.
This will necessitate a wide range of capabilities, including high-performance decryption, post-decryption deep packet inspection, detection of malicious URLs, identification of command and control operations, malware download, and threat correlation. These features, however, are CPU-intensive and are known for bringing even high-end commercial NGFWs to a halt.
Understand the responsibilities of encryption and certificates. And, as malware and threats grow more difficult to detect at the access point, security must be extended across the network to monitor behaviors and reveal intent.
For administration, use the GUI and CLI. Furthermore, these security strategies can achieve roles such as firewalls, web filtering, intrusion detection, and malware or spam prevention. Prepare the professional for the implementation of corporate security policies and the strengthening of network security programs. According to the latest Anti-Phishing Working Group (APWG) report, SSL was employed by 75% of all phishing sites in the first quarter of 2020.